Among other things, single sign-on allows you to:
- reduce the use of multiple passwords: one password for “X” configured applications
- Improve the user experience
- facilitate the work of the company’s information systems management: the user will no longer have the annoying tendency to use weak passwords for example.
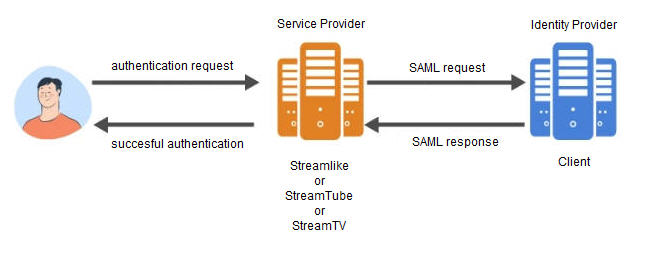
In a very simplified way, we can schematize the operation below:
- The user enters his identifiers and makes an authentication request
- The authentication authority checks the sent elements and validates or not the request. If all is validated within the directory then the authority returns a token of identification. This token gives access to all the requested applications.
- The user has access to his applications / tools.
We have the choice in the use of several protocols in the “small” world of single sign-on but two protocols seem to stand out:
Security Assertion Markup Language (SAML): protocol favored by many web applications. SAML relies on the use of XML certificates to accept authentication between :
- an Identity Provider: processes and validates the user’s authentication. It then sends back to the service provider the user information and the associated access rights
- and a Service Provider: receives the authentication validation from the Identity Provider
OAuth2: is a standard that gives authorizations to users. Major difference between the SAML protocol which manages the authentication.
In practice, single sign-on allows a user to seamlessly access all of the business applications in their organization without logging in each time. These applications do not know who the users are, but they do know if they should be given access and the extent of their rights. User management remains under the exclusive control of the customer who can create, modify or revoke rights for his employees.
We can support you in your single sign-on policy because all our solutions (“back” like StreamTube and “front” like StreamTV) are compatible with the SAML protocol.
Contact us to discuss this.
